Data Discovery and Classification - Policy Management
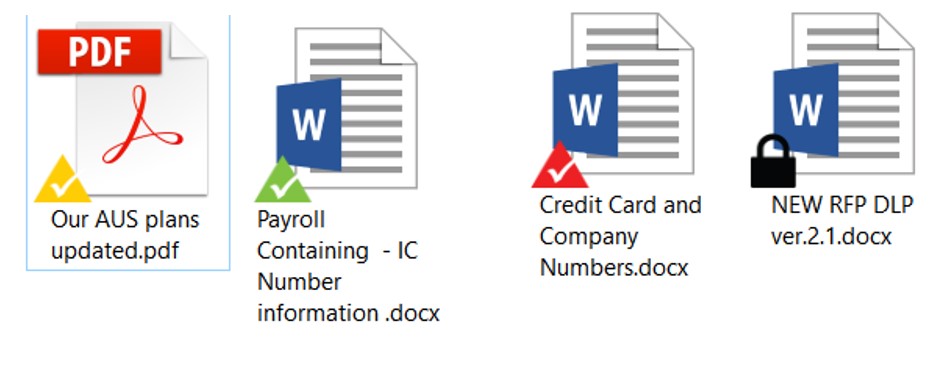
e-Safe Compliance provides the ability to discover and classify data in various forms for data sets e.g. text, alphanumeric, regular expressions, by file extension, by location and source code. These data sets can be gathered from various sources. Some of the notable ones include the following:
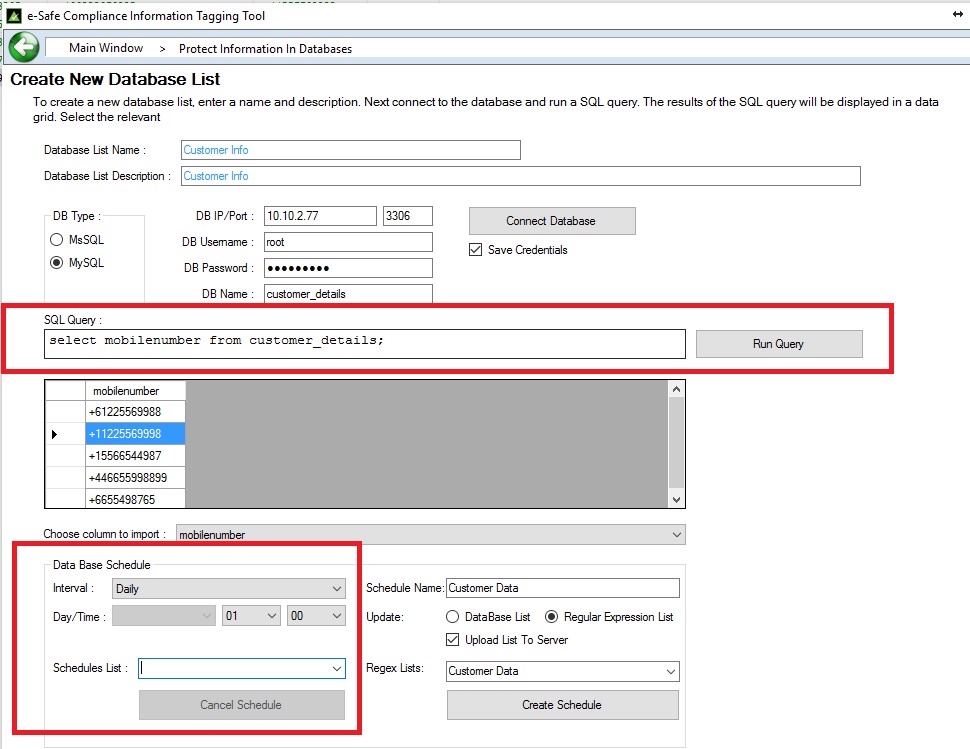
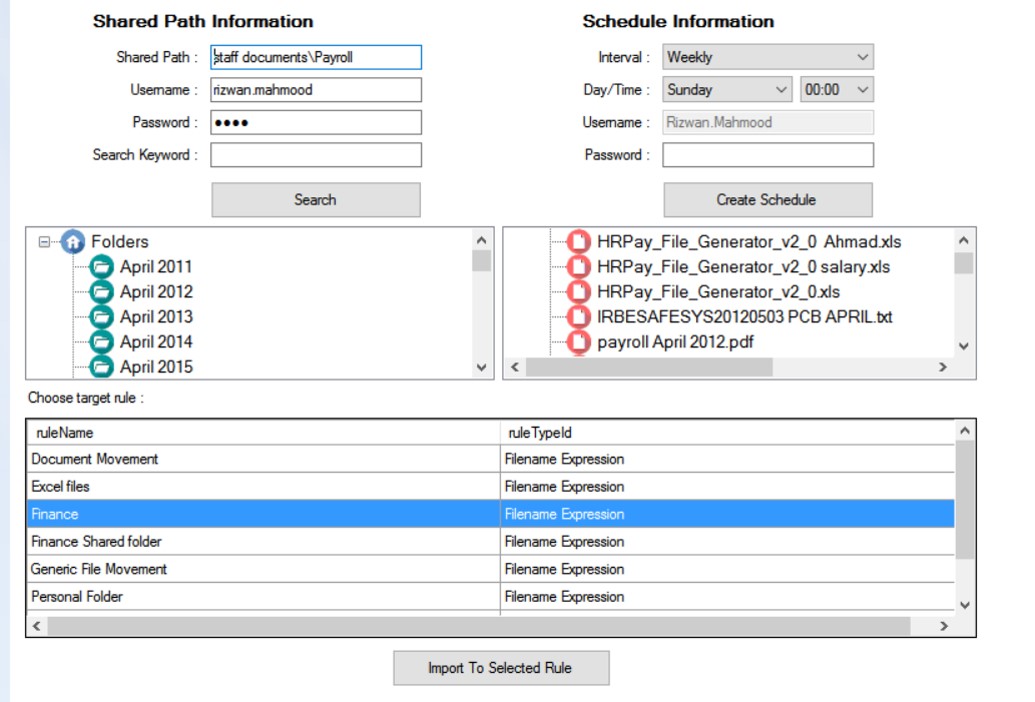
- Identification and classification of data in file repositories (shared drives / file servers) and from Databases and Document Management Systems using SQL statements. Such as categorizing personal identity numbers and other IP related data.
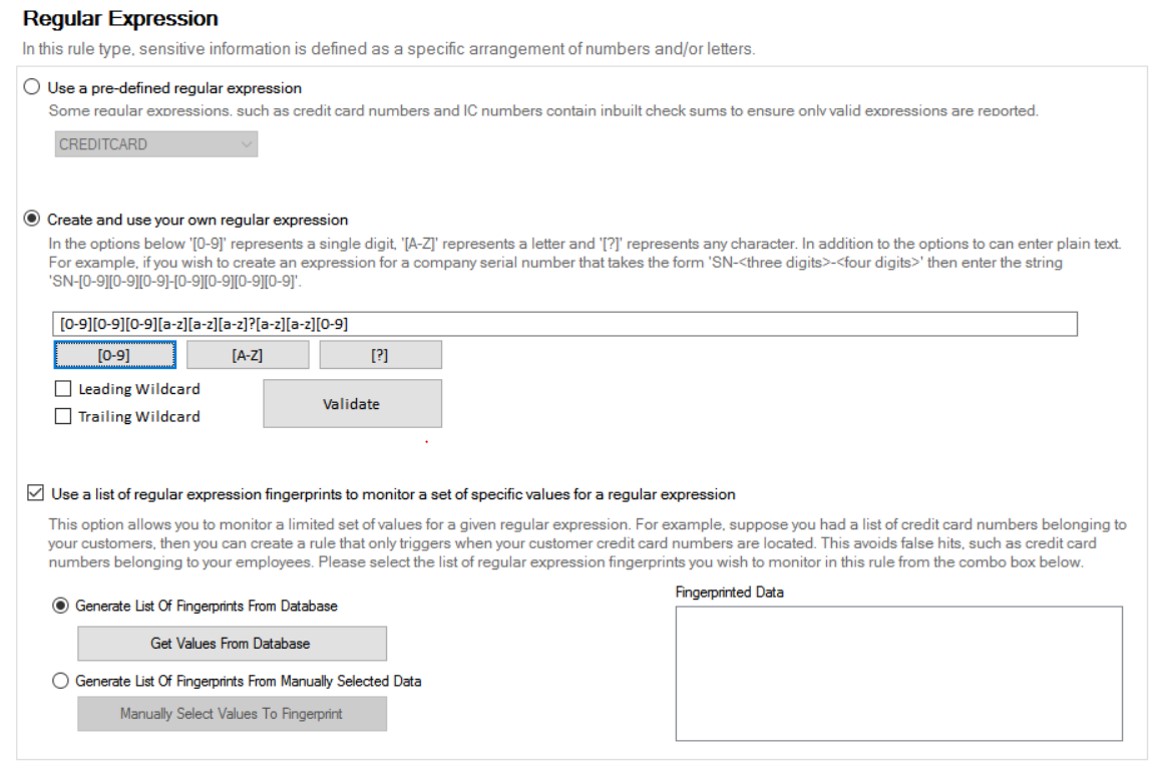
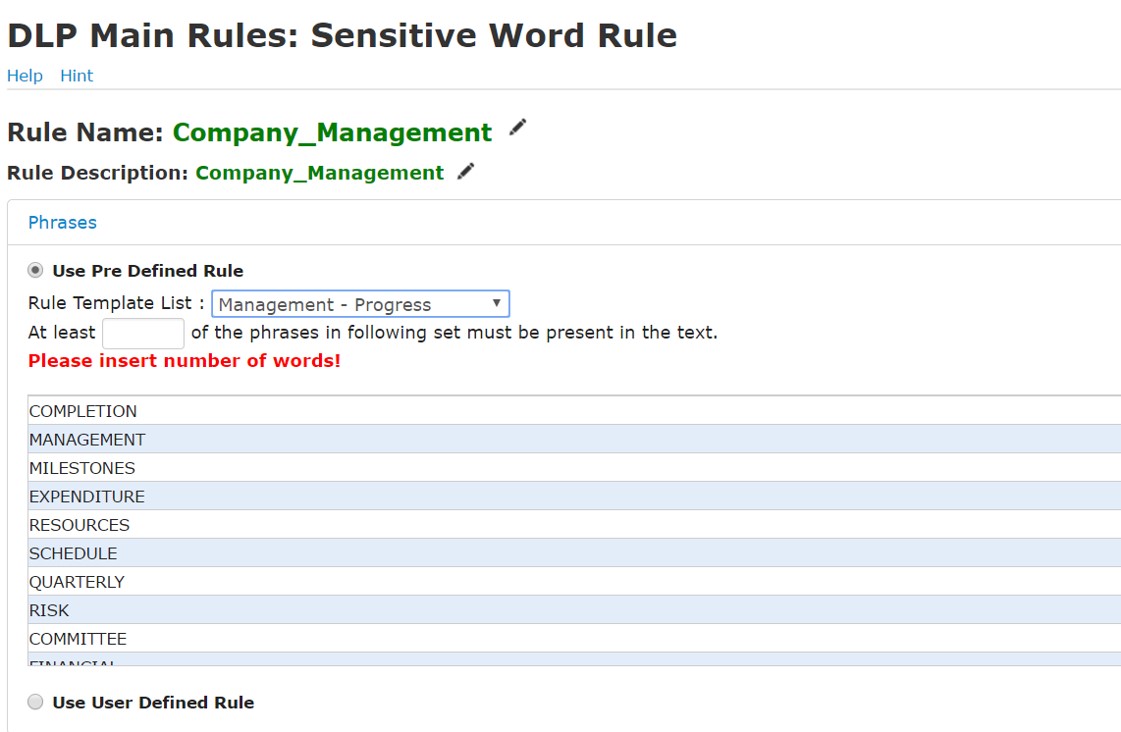
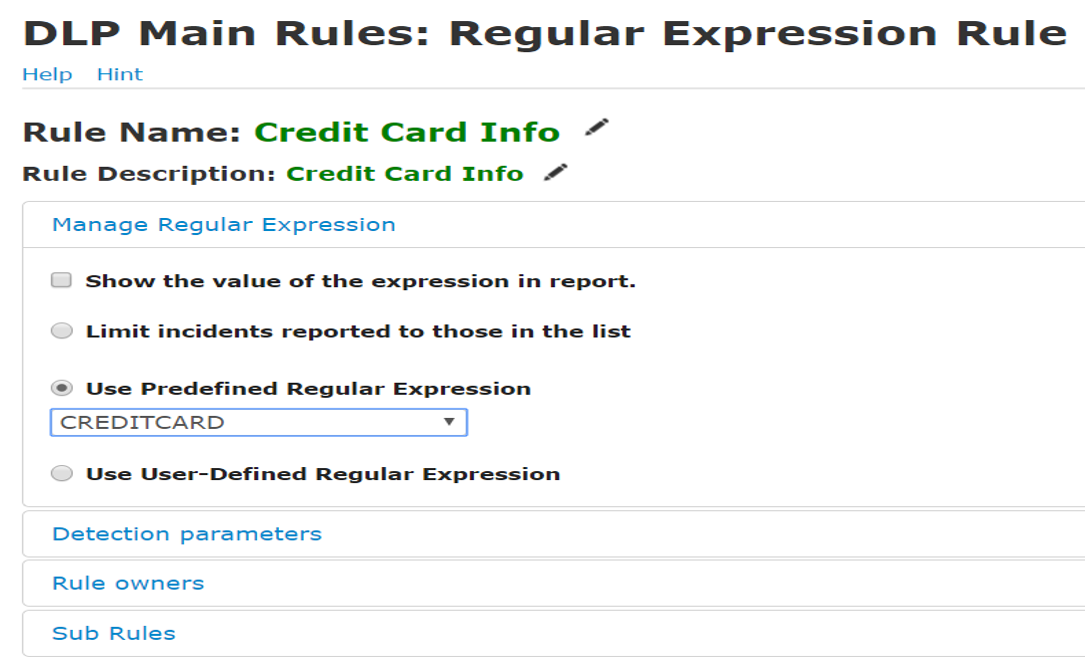
- Predefined templates for various data sets (e.g. finance, HR, etc) and regular expressions (e.g credit card, PII data etc) for easy classification of the environment
- Sticky classification by location – information sensitivity linked to its presence in specific file stores. Classification follows even if information moved.
- From existing lists of data – list of IDs, Medicare numbers, Credit card numbers etc to ensure targeted security
- Fed in via information owners – through decentralized tools to add adhoc data and specify its usage
- Discovery and classification of data at rest (end-points and servers) , in use and data in motion across the network – e.g. on cloud drives (Dropbox, G drive etc), free mails (Gmail etc), encrypted chats and encrypted websites
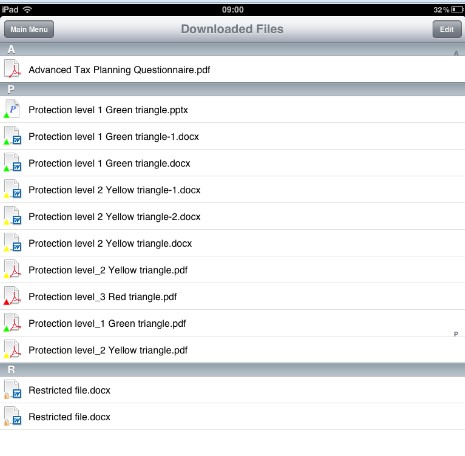
- Discovery and classification of files in mobile devices and with external 3rd party users via e-Safe 3rd part interaction application and e-Safe Mobile APP
Data Security Controls - Policy Management
e-Safe Compliance provides admin easy to use centralized data policy security management options to control the identified datasets. Some of the key features include:
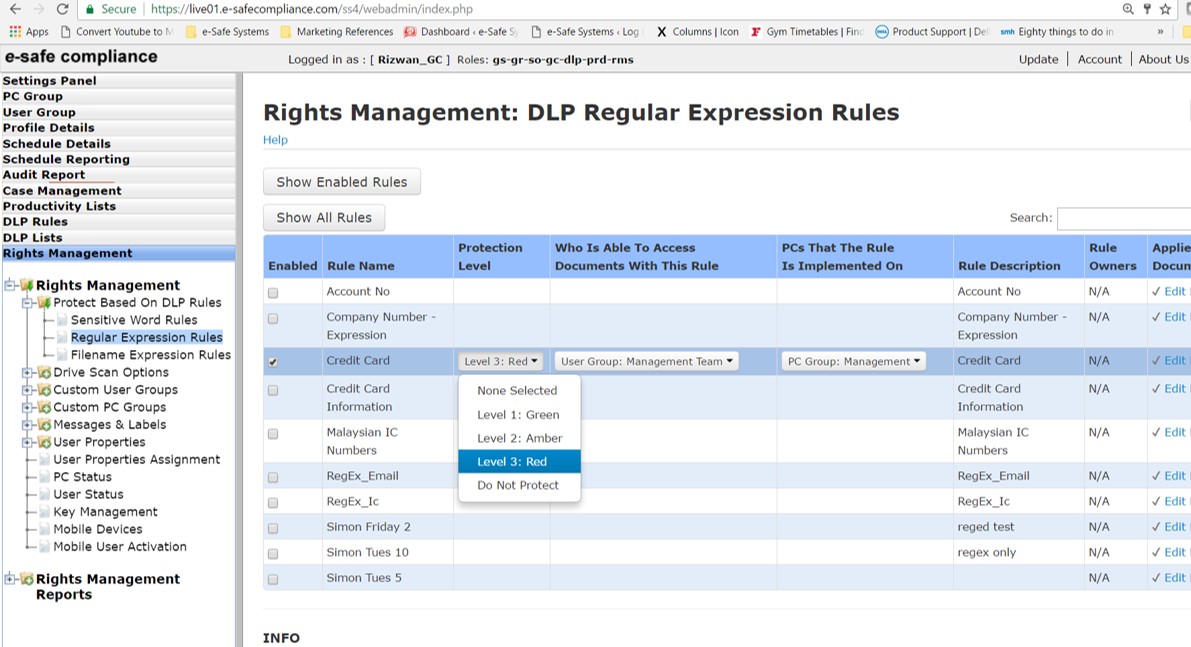
- Creation of central protection schemes irrespective of data store based on data sensitivity
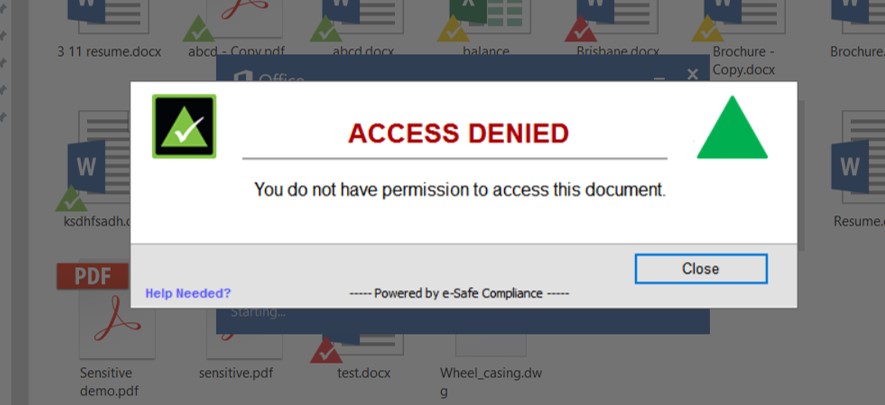
- Creation of access rights based on information related to specific user / user groups and pc/pc groups
- Integration / synching with AD to gather users and user roles within the organisation.
- Control over user rights and privileges based on user type
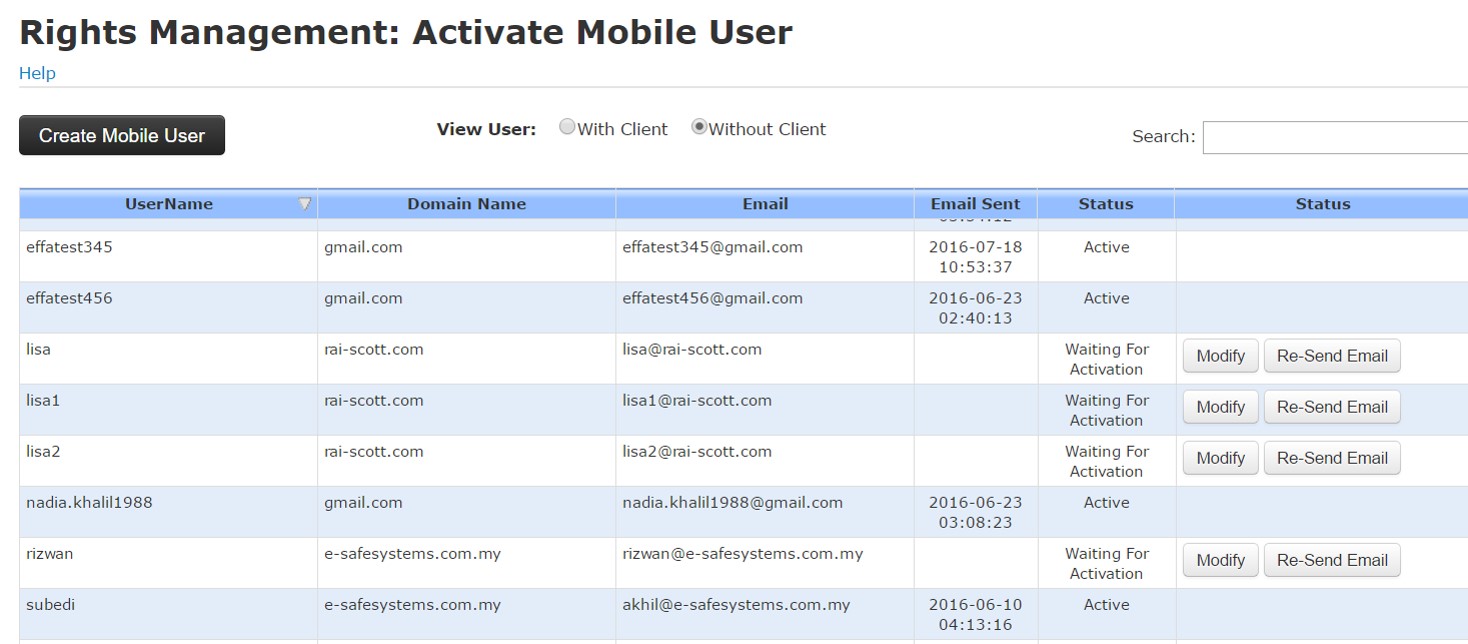
- Central control for mobile and external 3rd party users
- Establishing special measures to handle data with ex-employees, high risk users and stolen sensitive devices
- Support for multiple roles within system, based on ISO27001, to ensure separation of duties and allow for auditing of system usage.
Data Protection
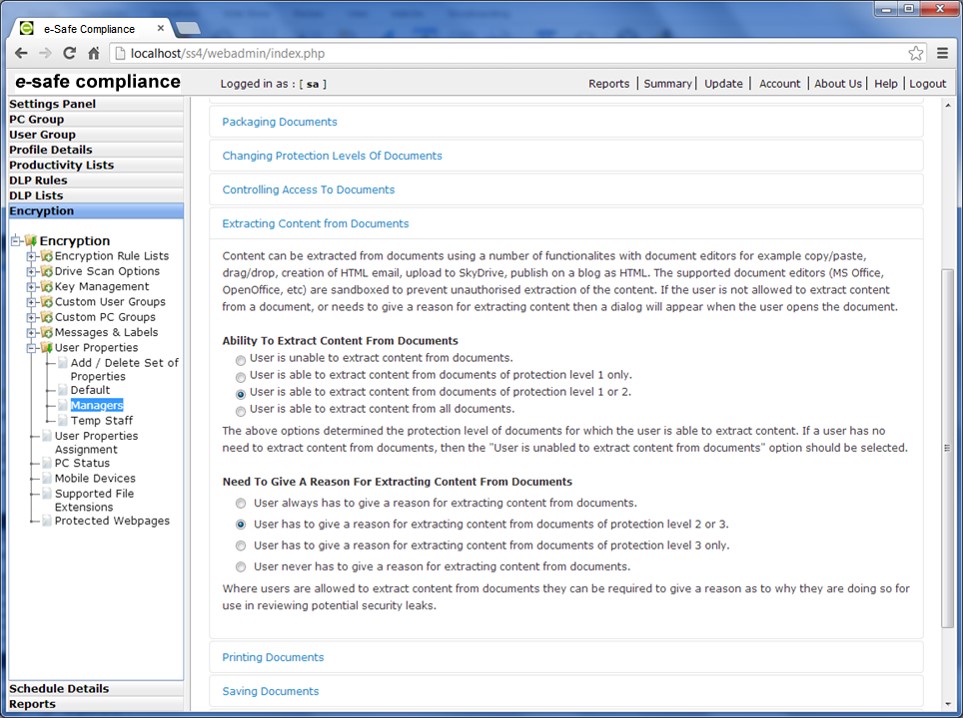
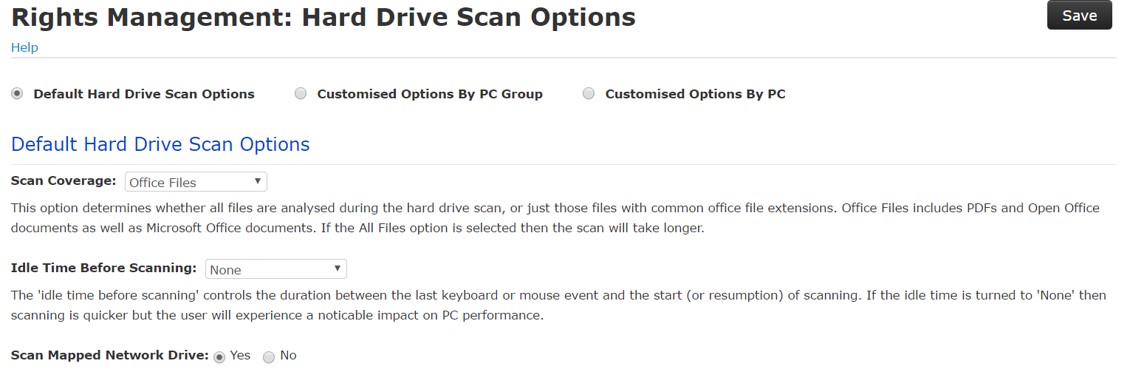
Persistent and transparent encryption to automatically secure sensitive documents based on rules. Key features include:
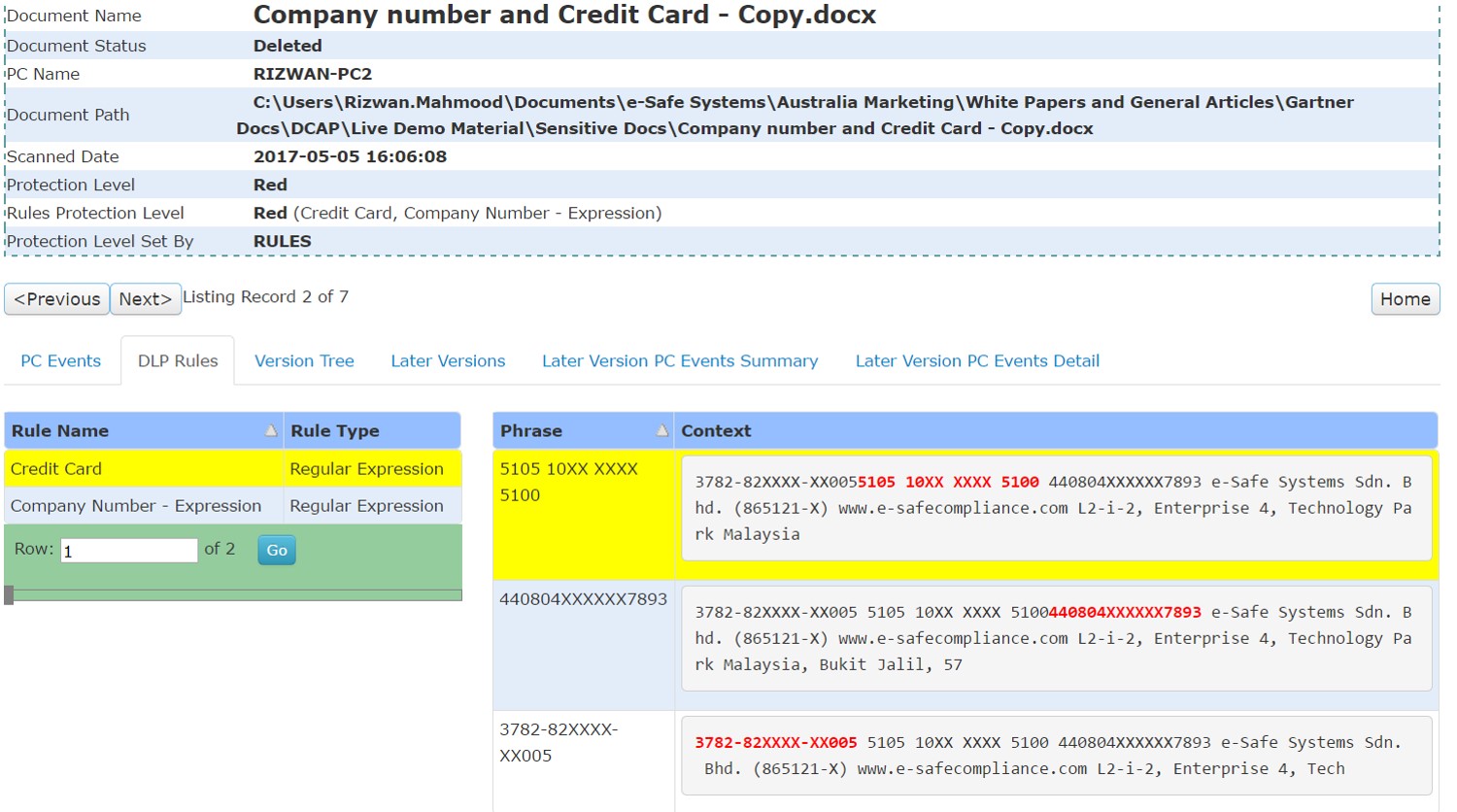
- Automatic classification and protection of data in files upon discovery using classification rules
- Can only be accessed on PCs having e-Safe agent installed with the relevant permissions
- Remains protected even if data leaves the organization
- Remains secured even if 1)if renamed 2)copies made 3)Saved in different formats 4) extensions removed
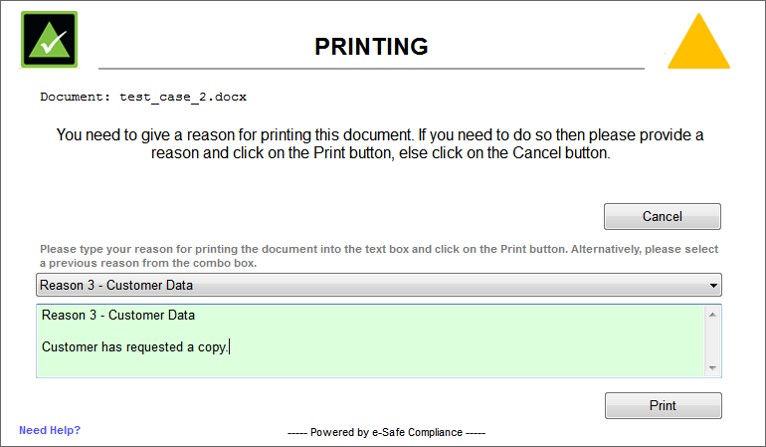
- Usage Management to block copy/paste, printing, screen grabs depending on sensitivity level of file content.
- Built in user rights management to control access to data
- Special options to protect data in Mobile, BYOD and with 3rd parties
Data Auditing and Activity Monitoring
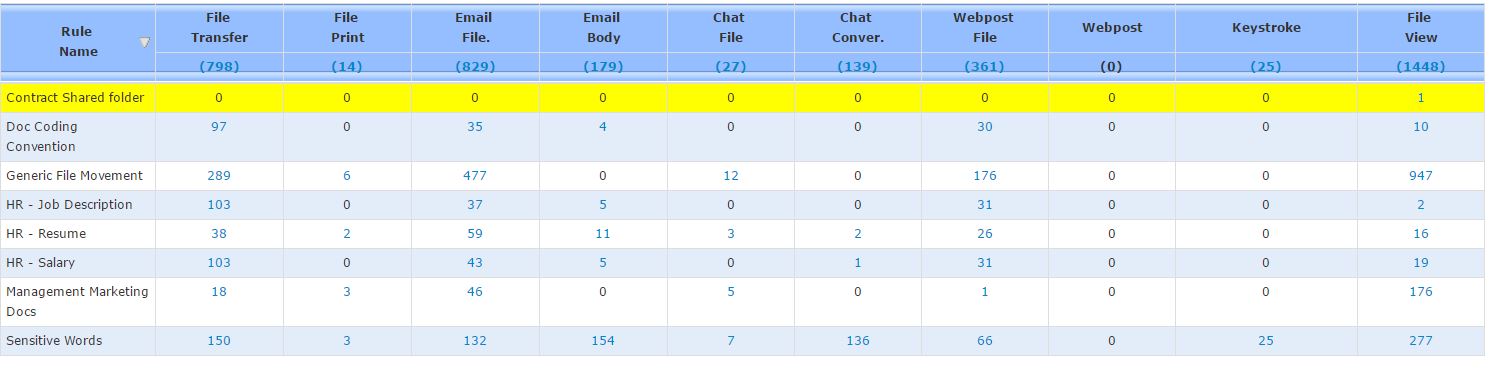
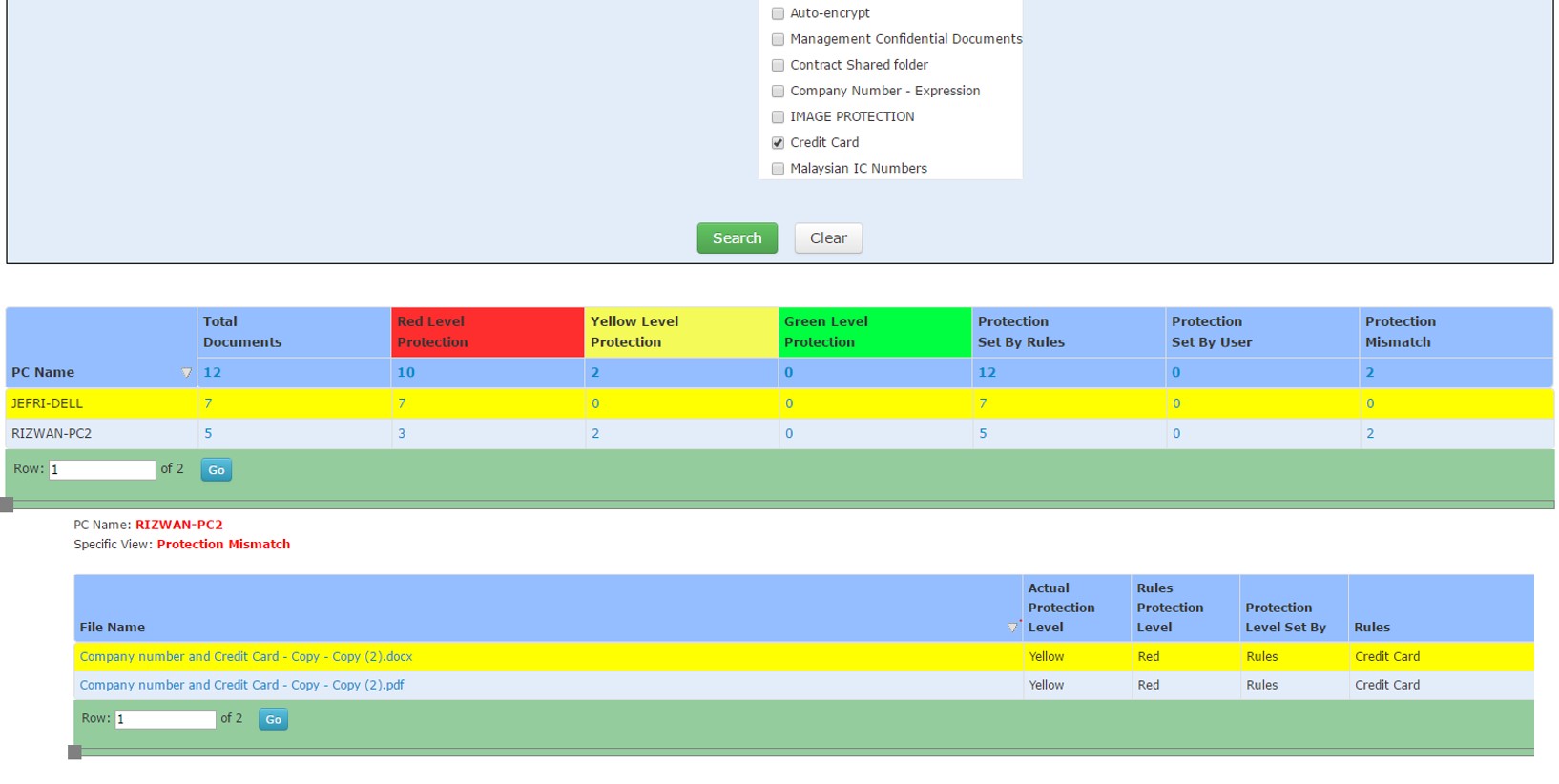
e-Safe Compliance offers total visibility on the access, usage, movement, deletion of datasets from the perspective of the dataset, end-user and end-point. Some of the key features include:
- Monitoring movement of specific datasets via corporate or non-corporate means. This includes 1) Online means - free cloud applications, corporate applications, free cloud drives, websites, chats, free emails, social media etc. 2) Offline means – USB, SD cards, syncing to phones and printing
- Incident report system which allows different types of incidents to be amalgamated and commented on for further action.
- Monitoring complete life cycle of all versions of the dataset which includes location, movement, deletion, opening and editing
- Drill down reporting from statistical overview of user activity down to file content itself.
- Identifying malicious action by users such as renaming files having sensitive datasets
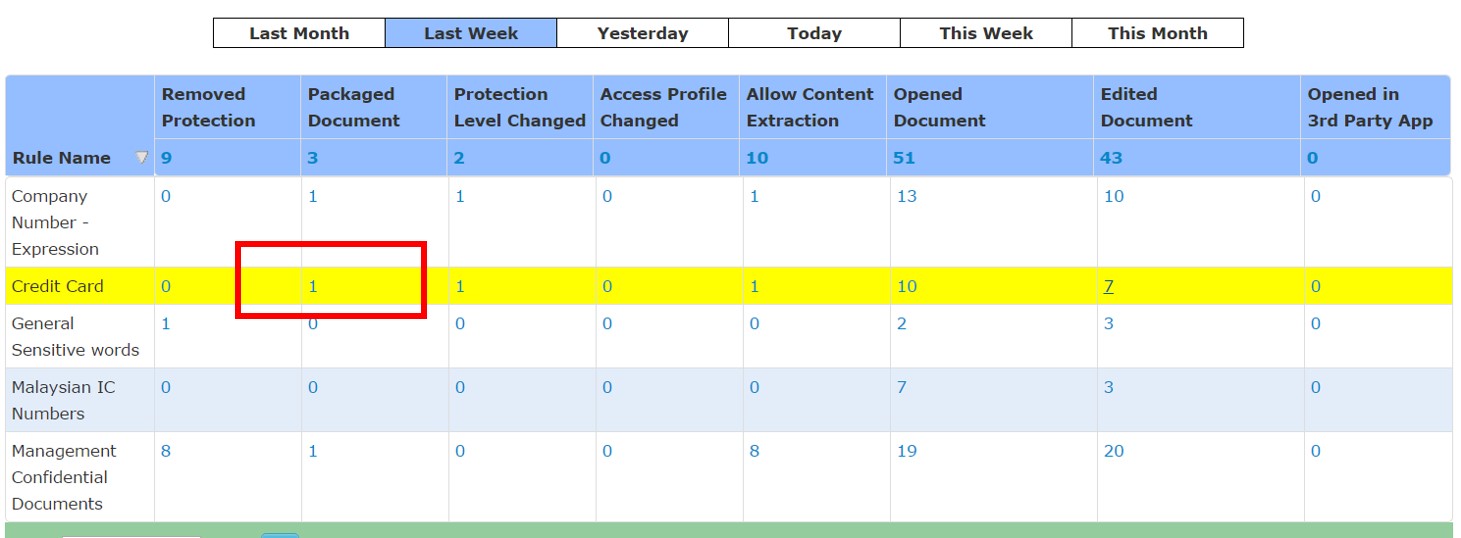
Data Centric - User Behaviour Analytics
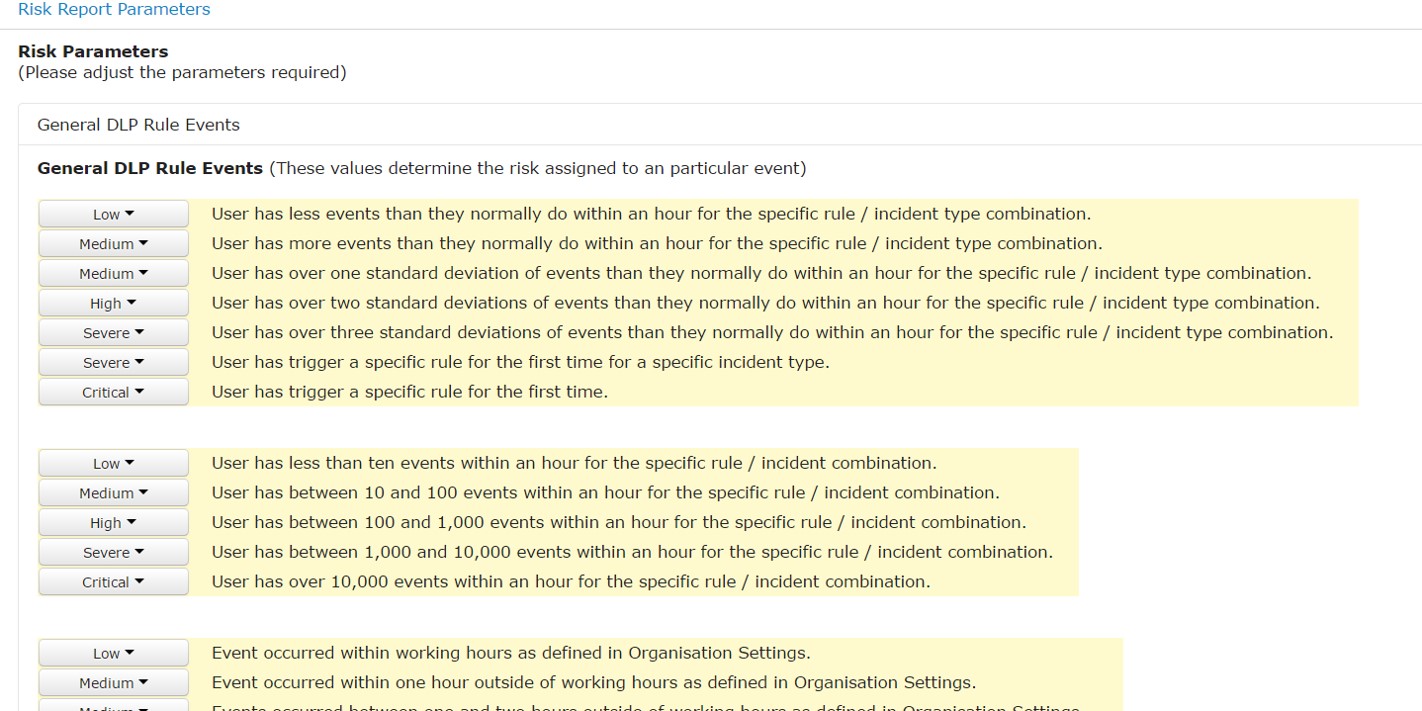
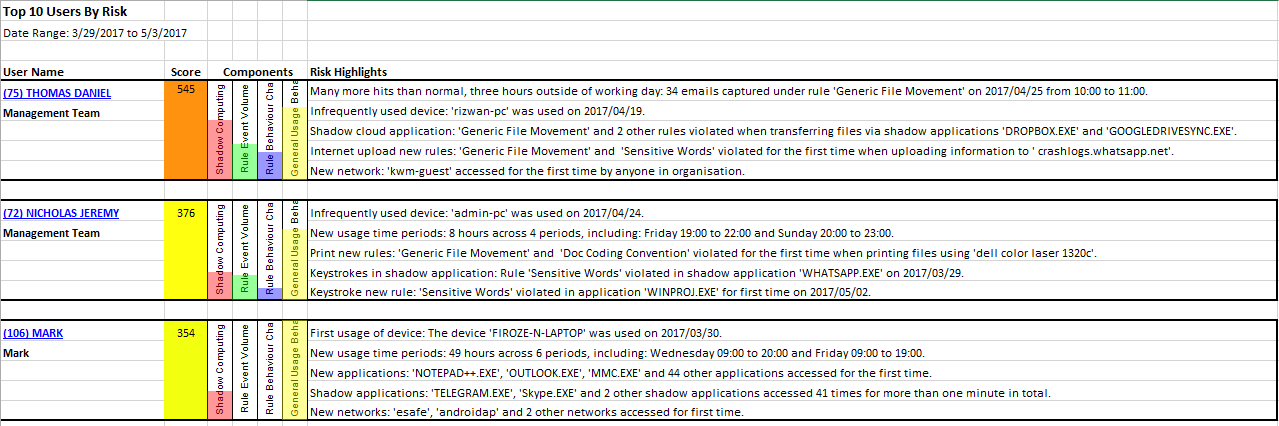
User behaviour analytics helps to make sense of the large number of data auditing reports being produced by the e-Safe system. The risk based reporting helps the admin to home in on serious issues which require quick action. Further it helps to establish user data usage patterns which helps to find malicious use of sensitive data over time and as user behaviour changes. Key features include:
- Ability to define risk level for different user scenarios and use cases based on the usage of the sensitive data sets
- Using artificial intelligence to establish a user behaviour base line and report on risky changes in behaviours over time. Like sensitive customer credit card information is normally never printed by anyone in the finance department but one user decides to print it for the first time.
- Behaviour risk reporting highlighting areas of concern in plain English to direct attention to information owners.
- Risk scores help to establish top risky users and top risky behaviours.