Solution : e-Safe Compliance Educates and Modifies Human Behaviour
1. Visual signals ensure ongoing education and ensure compliance
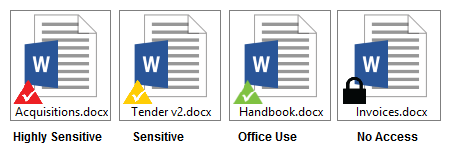
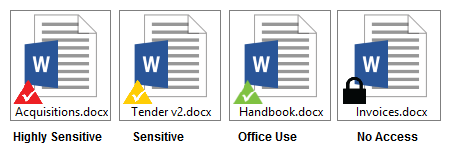
e-Safe Compliance assists in improving the behaviour of users by educating the users on acceptable usage. e-Safe Compliance monitors user behaviour, and when misuse of sensitive information or inappropriate behaviour is found, it displays warning messages to the user for guidance. For example, sensitive information is clearly marked with triangles based on their sensitivity levels (displayed below). The visual representation ensures users are aware they are dealing with sensitive information and appropriate warning messages are displayed when they mishandle the information.
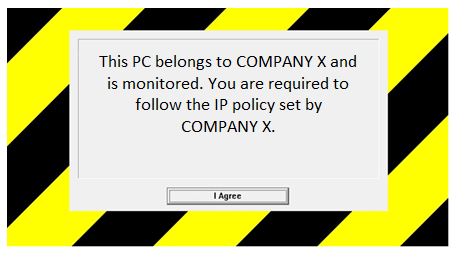
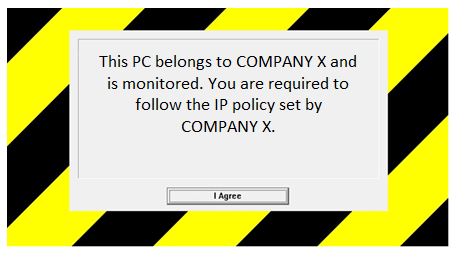
In addition to this, users are warned of any misuse of the company property through the display of a clear policy screen when logging into the company’s PC
. This policy screen (displayed below) sends a clear, customisable message to members of staff that this machine is monitored and thus acts as a perfect deterrent to prevent infringement of the company’s IT policy.
2. Automatic feedback mechanism to improve monitoring
e-Safe Compliance offers an easy way for users to give feedback and, where authorised, allows the user to
override a restriction by giving a reason. Traditional security systems have two modes of operation: i) restrict document usage, and ii) allow document usage but monitor.

Restricting document usage prevents users from doing their job, while just monitoring document usage results in the reviewing of a large number of incidents. e-Safe Compliance introduces a third way – “allow users to remove restrictions but require them to provide a reason for doing so.” By allowing authorised users to override restrictions, the users are no longer prevented from doing their job. Furthermore, the reason is used to better tag the sensitive document in future, based on its usage. Most importantly, the override and the reason given are reported directly to the information owner, who will either accept, or choose to investigate, if the behaviour is suspicious.